19 KiB
| stage | group | info | disqus_identifier | type |
|---|---|---|---|---|
| Verify | Continuous Integration | To determine the technical writer assigned to the Stage/Group associated with this page, see https://about.gitlab.com/handbook/engineering/ux/technical-writing/#designated-technical-writers | https://docs.gitlab.com/ee/user/project/pipelines/job_artifacts.html | reference, howto |
Job artifacts
- Introduced in GitLab 8.2 and GitLab Runner 0.7.0.
- Starting with GitLab 8.4 and GitLab Runner 1.0, the artifacts archive format changed to
ZIP, and it's now possible to browse its contents, with the added ability of downloading the files separately.- In GitLab 8.17, builds were renamed to jobs.
- The artifacts browser will be available only for new artifacts that are sent to GitLab using GitLab Runner version 1.0 and up. It won't be possible to browse old artifacts already uploaded to GitLab.
Job artifacts are a list of files and directories created by a job once it finishes. This feature is enabled by default in all GitLab installations.
Job artifacts created by GitLab Runner are uploaded to GitLab and are downloadable as a single archive using the GitLab UI or the GitLab API.
For an overview, watch the video GitLab CI Pipeline, Artifacts, and Environments. Watch also GitLab CI pipeline tutorial for beginners.
Defining artifacts in .gitlab-ci.yml
A simple example of using the artifacts definition in .gitlab-ci.yml would be
the following:
pdf:
script: xelatex mycv.tex
artifacts:
paths:
- mycv.pdf
expire_in: 1 week
A job named pdf calls the xelatex command in order to build a PDF file from
the latex source file mycv.tex. We then define the artifacts paths which in
turn are defined with the paths keyword. All paths to files and directories
are relative to the repository that was cloned during the build.
The artifacts will be uploaded when the job succeeds by default, but can be set to upload
when the job fails, or always, if the artifacts:when
parameter is used. These uploaded artifacts will be kept in GitLab for 1 week as defined
by the expire_in definition. You can keep the artifacts from expiring
via the web interface. If the expiry time is not defined, it defaults
to the instance wide setting.
For more examples on artifacts, follow the artifacts reference in
.gitlab-ci.yml.
artifacts:reports
- Introduced in GitLab 11.2.
- Requires GitLab Runner 11.2 and above.
The artifacts:reports keyword is used for collecting test reports, code quality
reports, and security reports from jobs. It also exposes these reports in GitLab's
UI (merge requests, pipeline views, and security dashboards).
NOTE: Note:
The test reports are collected regardless of the job results (success or failure).
You can use artifacts:expire_in to set up an expiration
date for their artifacts.
NOTE: Note:
If you also want the ability to browse the report output files, include the
artifacts:paths keyword.
artifacts:reports:junit
- Introduced in GitLab 11.2.
- Requires GitLab Runner 11.2 and above.
The junit report collects JUnit XML files
as artifacts. Although JUnit was originally developed in Java, there are many
third party ports for other
languages like JavaScript, Python, Ruby, and so on.
See JUnit test reports for more details and examples. Below is an example of collecting a JUnit XML file from Ruby's RSpec test tool:
rspec:
stage: test
script:
- bundle install
- rspec --format RspecJunitFormatter --out rspec.xml
artifacts:
reports:
junit: rspec.xml
The collected JUnit reports will be uploaded to GitLab as an artifact and will be automatically shown in merge requests.
NOTE: Note:
In case the JUnit tool you use exports to multiple XML files, you can specify
multiple test report paths within a single job and they will be automatically
concatenated into a single file. Use a filename pattern (junit: rspec-*.xml),
an array of filenames (junit: [rspec-1.xml, rspec-2.xml, rspec-3.xml]), or a
combination thereof (junit: [rspec.xml, test-results/TEST-*.xml]).
artifacts:reports:dotenv
- Introduced in GitLab 12.9.
- Requires GitLab Runner 11.5 and later.
The dotenv report collects a set of environment variables as artifacts.
The collected variables are registered as runtime-created variables of the job, which is useful to set dynamic environment URLs after a job finishes.
There are a couple of exceptions to the original dotenv rules:
- The variable key can contain only letters, digits, and underscores (
_). - The maximum size of the
.envfile is 5 KB. - The maximum number of variables is 10.
- Variable substitution in the
.envfile is not supported. - The
.envfile can't have empty lines or comments (starting with#). - Key values in the
envfile cannot have spaces or newline characters (\n), including when using single or double quotes. - Quote escaping during parsing (
key = 'value'->{key: "value"}) is not supported.
artifacts:reports:cobertura
- Introduced in GitLab 12.9.
- Requires GitLab Runner 11.5 and above.
The cobertura report collects Cobertura coverage XML files.
The collected Cobertura coverage reports will be uploaded to GitLab as an artifact
and will be automatically shown in merge requests.
Cobertura was originally developed for Java, but there are many third party ports for other languages like JavaScript, Python, Ruby, and so on.
artifacts:reports:terraform
- Introduced in GitLab 13.0.
- Requires GitLab Runner 11.5 and above.
The terraform report obtains a Terraform tfplan.json file. JQ processing required to remove credentials. The collected Terraform
plan report will be uploaded to GitLab as an artifact and will be automatically shown
in merge requests. For more information, see
Output terraform plan information into a merge request.
artifacts:reports:codequality
- Introduced in GitLab Starter 11.5.
- Made available in all tiers in GitLab 13.2.
- Requires GitLab Runner 11.5 and above.
The codequality report collects CodeQuality issues
as artifacts.
The collected Code Quality report will be uploaded to GitLab as an artifact and will be summarized in merge requests.
artifacts:reports:sast (ULTIMATE)
- Introduced in GitLab 11.5.
- Requires GitLab Runner 11.5 and above.
The sast report collects SAST vulnerabilities
as artifacts.
The collected SAST report will be uploaded to GitLab as an artifact and will be summarized in the merge requests and pipeline view. It's also used to provide data for security dashboards.
artifacts:reports:secret_detection (ULTIMATE)
- Introduced in GitLab 13.1.
- Requires GitLab Runner 11.5 and above.
The secret-detection report collects detected secrets
as artifacts.
The collected Secret Detection report is uploaded to GitLab as an artifact and summarized in the merge requests and pipeline view. It's also used to provide data for security dashboards.
artifacts:reports:dependency_scanning (ULTIMATE)
- Introduced in GitLab 11.5.
- Requires GitLab Runner 11.5 and above.
The dependency_scanning report collects Dependency Scanning vulnerabilities
as artifacts.
The collected Dependency Scanning report will be uploaded to GitLab as an artifact and will be summarized in the merge requests and pipeline view. It's also used to provide data for security dashboards.
artifacts:reports:container_scanning (ULTIMATE)
- Introduced in GitLab 11.5.
- Requires GitLab Runner 11.5 and above.
The container_scanning report collects Container Scanning vulnerabilities
as artifacts.
The collected Container Scanning report will be uploaded to GitLab as an artifact and will be summarized in the merge requests and pipeline view. It's also used to provide data for security dashboards.
artifacts:reports:dast (ULTIMATE)
- Introduced in GitLab 11.5.
- Requires GitLab Runner 11.5 and above.
The dast report collects DAST vulnerabilities
as artifacts.
The collected DAST report will be uploaded to GitLab as an artifact and will be summarized in the merge requests and pipeline view. It's also used to provide data for security dashboards.
artifacts:reports:license_management (ULTIMATE)
- Introduced in GitLab 11.5.
- Requires GitLab Runner 11.5 and above.
CAUTION: Warning: This artifact is still valid but is deprecated in favor of the artifacts:reports:license_scanning introduced in GitLab 12.8.
The license_management report collects Licenses
as artifacts.
The collected License Compliance report will be uploaded to GitLab as an artifact and will be summarized in the merge requests and pipeline view. It's also used to provide data for security dashboards.
artifacts:reports:license_scanning (ULTIMATE)
- Introduced in GitLab 12.8.
- Requires GitLab Runner 11.5 and above.
The license_scanning report collects Licenses
as artifacts.
The License Compliance report will be uploaded to GitLab as an artifact and will be automatically shown in merge requests, pipeline view and provide data for security dashboards.
artifacts:reports:performance (PREMIUM)
- Introduced in GitLab 11.5.
- Requires GitLab Runner 11.5 and above.
The performance report collects Browser Performance Testing metrics
as artifacts.
The collected Browser Performance report will be uploaded to GitLab as an artifact and will be automatically shown in merge requests.
artifacts:reports:load_performance (PREMIUM)
- Introduced in GitLab 13.2 in GitLab Premium 13.2.
- Requires GitLab Runner 11.5 and above.
The load_performance report collects Load Performance Testing metrics
as artifacts.
The report is uploaded to GitLab as an artifact and is shown in merge requests automatically.
artifacts:reports:metrics (PREMIUM)
Introduced in GitLab 11.10.
The metrics report collects Metrics
as artifacts.
The collected Metrics report will be uploaded to GitLab as an artifact and will be automatically shown in merge requests.
artifacts:reports:requirements (ULTIMATE)
- Introduced in GitLab 13.1.
- Requires GitLab Runner 11.5 and above.
The requirements report collects requirements.json files as artifacts.
The collected Requirements report will be uploaded to GitLab as an artifact and existing requirements will be marked as Satisfied.
Browsing artifacts
- From GitLab 9.2, PDFs, images, videos, and other formats can be previewed directly in the job artifacts browser without the need to download them.
- Introduced in GitLab 10.1, HTML files in a public project can be previewed directly in a new tab without the need to download them when GitLab Pages is enabled. The same applies for textual formats (currently supported extensions:
.txt,.json, and.log).- Introduced in GitLab 12.4, artifacts in private projects can be previewed when GitLab Pages access control is enabled.
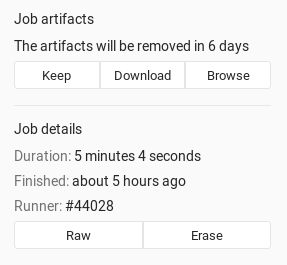
After a job finishes, if you visit the job's specific page, there are three buttons. You can download the artifacts archive or browse its contents, whereas the Keep button appears only if you've set an expiry date to the artifacts in case you changed your mind and want to keep them.
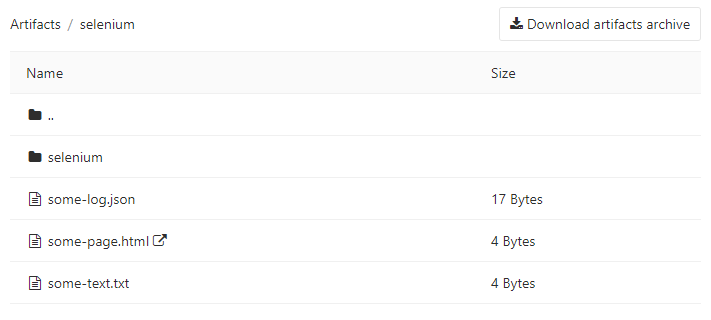
The archive browser shows the name and the actual file size of each file in the archive. If your artifacts contained directories, then you're also able to browse inside them.
Below you can see what browsing looks like. In this case we have browsed inside the archive and at this point there is one directory, a couple files, and one HTML file that you can view directly online when GitLab Pages is enabled (opens in a new tab).
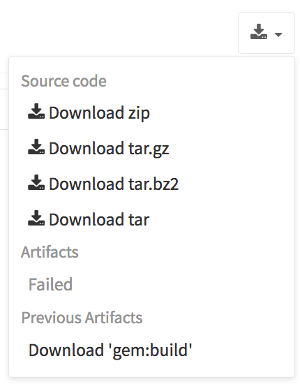
Downloading artifacts
If you need to download an artifact or the whole archive, there are buttons in various places in the GitLab UI to do this:
-
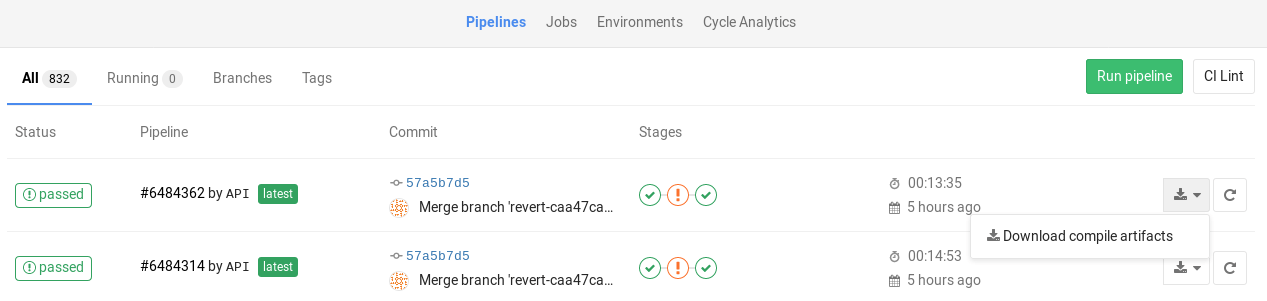
While on the pipelines page, you can see the download icon for each job's artifacts and archive in the right corner:
-
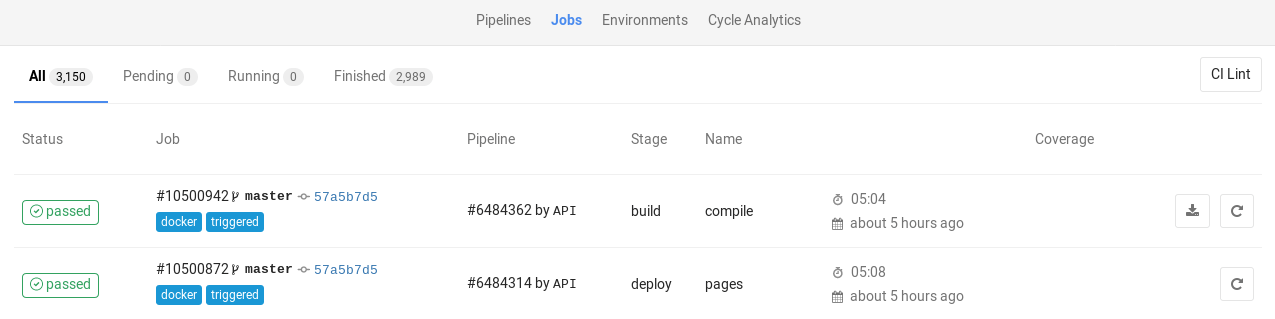
While on the Jobs page, you can see the download icon for each job's artifacts and archive in the right corner:
-
While inside a specific job, you're presented with a download button along with the one that browses the archive:
-
And finally, when browsing an archive you can see the download button at the top right corner:
Downloading the latest artifacts
It's possible to download the latest artifacts of a job via a well known URL so you can use it for scripting purposes.
NOTE: Note: The latest artifacts are created by jobs in the most recent successful pipeline for the specific ref. If you run two types of pipelines for the same ref, the latest artifact will be determined by timing. For example, if a branch pipeline created by merging a merge request runs at the same time as a scheduled pipeline, the latest artifact will be from the pipeline that completed most recently.
Artifacts for other pipelines can be accessed with direct access to them.
The structure of the URL to download the whole artifacts archive is the following:
https://example.com/<namespace>/<project>/-/jobs/artifacts/<ref>/download?job=<job_name>
To download a single file from the artifacts use the following URL:
https://example.com/<namespace>/<project>/-/jobs/artifacts/<ref>/raw/<path_to_file>?job=<job_name>
For example, to download the latest artifacts of the job named coverage of
the master branch of the gitlab project that belongs to the gitlab-org
namespace, the URL would be:
https://gitlab.com/gitlab-org/gitlab/-/jobs/artifacts/master/download?job=coverage
To download the file coverage/index.html from the same
artifacts use the following URL:
https://gitlab.com/gitlab-org/gitlab/-/jobs/artifacts/master/raw/coverage/index.html?job=coverage
There is also a URL to browse the latest job artifacts:
https://example.com/<namespace>/<project>/-/jobs/artifacts/<ref>/browse?job=<job_name>
For example:
https://gitlab.com/gitlab-org/gitlab/-/jobs/artifacts/master/browse?job=coverage
There is also a URL to specific files, including HTML files that are shown in GitLab Pages:
https://example.com/<namespace>/<project>/-/jobs/artifacts/<ref>/file/<path>?job=<job_name>
For example, when a job coverage creates the artifact htmlcov/index.html,
you can access it at:
https://gitlab.com/gitlab-org/gitlab/-/jobs/artifacts/master/file/htmlcov/index.html?job=coverage
The latest builds are also exposed in the UI in various places. Specifically, look for the download button in:
- The main project's page
- The branches page
- The tags page
If the latest job has failed to upload the artifacts, you can see that information in the UI.
Erasing artifacts
DANGER: Danger: This is a destructive action that leads to data loss. Use with caution.
You can erase a single job via the UI, which will also remove the job's artifacts and trace, if you are:
- The owner of the job.
- A Maintainer of the project.
To erase a job:
- Navigate to a job's page.
- Click the trash icon at the top right of the job's trace.
- Confirm the deletion.
Retrieve artifacts of private projects when using GitLab CI
In order to retrieve a job artifact of a different project, you might need to use a private token in order to authenticate and download the artifacts.