6.8 KiB
| stage | group | info | type |
|---|---|---|---|
| Release | Progressive Delivery | To determine the technical writer assigned to the Stage/Group associated with this page, see https://about.gitlab.com/handbook/engineering/ux/technical-writing/#designated-technical-writers | howto |
Deploy Tokens
- Introduced in GitLab 10.7.
- Moved from Settings > Repository in GitLab 12.9.
- Added
write_registryscope in GitLab 12.10.- Moved from Settings > CI / CD in GitLab 12.10.1.
- Added package registry scopes from Settings > CI / CD in GitLab 13.0.
Deploy tokens allow you to download (git clone) or push and pull packages and container registry images of a project without having a user and a password.
Deploy tokens can be managed by maintainers only.
If you have a key pair, you might want to use deploy keys instead.
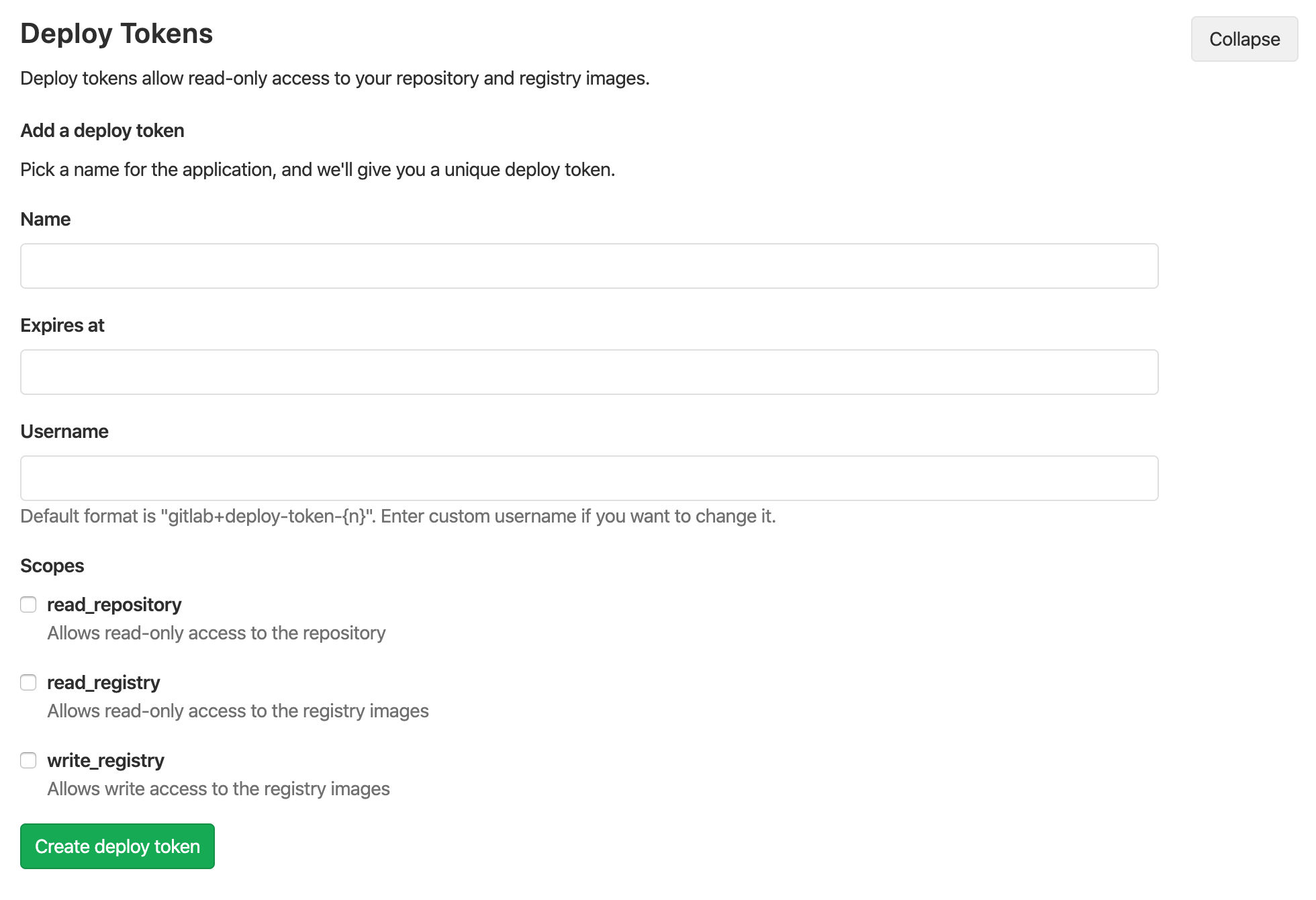
Creating a Deploy Token
You can create as many deploy tokens as you like from the settings of your project. Alternatively, you can also create group-scoped deploy tokens.
- Log in to your GitLab account.
- Go to the project (or group) you want to create Deploy Tokens for.
- Go to {settings} Settings > Repository.
- Click on "Expand" on Deploy Tokens section.
- Choose a name, expiry date (optional), and username (optional) for the token.
- Choose the desired scopes.
- Click on Create deploy token.
- Save the deploy token somewhere safe. Once you leave or refresh the page, you won't be able to access it again.
Deploy token expiration
Deploy tokens expire on the date you define, at midnight UTC.
Revoking a deploy token
At any time, you can revoke any deploy token by just clicking the respective Revoke button under the 'Active deploy tokens' area.
Limiting scopes of a deploy token
Deploy tokens can be created with two different scopes that allow various actions that a given token can perform. The available scopes are depicted in the following table.
| Scope | Description |
|---|---|
read_repository |
Allows read-access to the repository through git clone |
read_registry |
Allows read-access to container registry images if a project is private and authorization is required. |
write_registry |
Allows write-access (push) to container registry. |
Deploy token custom username
Introduced in GitLab 12.1.
The default username format is gitlab+deploy-token-#{n}. Some tools or platforms may not support this format,
in such case you can specify custom username to be used when creating the deploy token.
Usage
Git clone a repository
To download a repository using a Deploy Token, you just need to:
-
Create a Deploy Token with
read_repositoryas a scope. -
Take note of your
usernameandtoken. -
git clonethe project using the Deploy Token:git clone https://<username>:<deploy_token>@gitlab.example.com/tanuki/awesome_project.git
Replace <username> and <deploy_token> with the proper values.
Read Container Registry images
To read the container registry images, you'll need to:
- Create a Deploy Token with
read_registryas a scope. - Take note of your
usernameandtoken. - Log in to GitLab’s Container Registry using the deploy token:
docker login -u <username> -p <deploy_token> registry.example.com
Just replace <username> and <deploy_token> with the proper values. Then you can simply
pull images from your Container Registry.
Push Container Registry images
To push the container registry images, you'll need to:
-
Create a Deploy Token with
write_registryas a scope. -
Take note of your
usernameandtoken. -
Log in to GitLab’s Container Registry using the deploy token:
docker login -u <username> -p <deploy_token> registry.example.com
Just replace <username> and <deploy_token> with the proper values. Then you can simply
push images to your Container Registry.
Read or pull packages
To pull packages in the GitLab package registry, you'll need to:
- Create a Deploy Token with
read_package_registryas a scope. - Take note of your
usernameandtoken. - For the package type of your choice, follow the authentication instructions for deploy tokens.
Push or upload packages
To upload packages in the GitLab package registry, you'll need to:
- Create a Deploy Token with
write_package_registryas a scope. - Take note of your
usernameandtoken. - For the package type of your choice, follow the authentication instructions for deploy tokens.
Group Deploy Token
Introduced in GitLab 12.9.
A deploy token created at the group level can be used across all projects that belong either to the specific group or to one of its subgroups.
For an overview, see Group Deploy Tokens.
To use a group deploy token:
- Create a deploy token for a group.
- Use it the same way you use a project deploy token when cloning a repository.
The scopes applied to a group deploy token (such as read_repository) will
apply consistently when cloning the repository of related projects.
GitLab Deploy Token
Introduced in GitLab 10.8.
There's a special case when it comes to Deploy Tokens. If a user creates one
named gitlab-deploy-token, the username and token of the Deploy Token will be
automatically exposed to the CI/CD jobs as environment variables: CI_DEPLOY_USER and
CI_DEPLOY_PASSWORD, respectively. With the GitLab Deploy Token, the
read_registry and write_registry scopes are implied.
After you create the token, you can login to the Container Registry using those variables:
docker login -u $CI_DEPLOY_USER -p $CI_DEPLOY_PASSWORD $CI_REGISTRY
NOTE: Note:
The special handling for the gitlab-deploy-token deploy token is not currently implemented for group deploy tokens. For the deploy token to be available for CI/CD jobs, it must be created at the project level. See this issue for details.